I wrote this article in Japanese and translated it into English using ChatGPT. I also used ChatGPT to create the English article title. I did my best to correct any translation mistakes, but please let me know if you find any errors. By the way, I did not use ChatGPT when writing the Japanese article. The entire article was written from scratch by me, Saikawa Goto.

Introduction
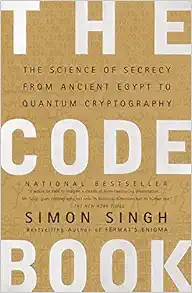
Movies and books covered in this article
Three takeaways from this article
- Without “cryptography”, modern civilization could not exist.
- Learn about classical cryptography used since ancient times, as well as the accompanying “key distribution problem”.
- Understand how “Public-key cryptography” solved “key distribution problem” and the major problem posed by quantum computers.
Self-introduction article
Published Kindle books(Free on Kindle Unlimited)
“The genius Einstein: An easy-to-understand book about interesting science advances that is not too simple based on his life and discoveries: Theory of Relativity, Cosmology and Quantum Theory”
“Why is “lack of imagination” called “communication skills”?: Japanese-specific”negative” communication”
The quotes in the article were translated using ChatGPT from Japanese books, and are not direct quotes from the foreign language original books, even if they exist.

The History of “Encryption” Drawn by the Best-Selling Author Simon Singh
“Encryption” is Indispensable in Modern Society
When you hear the word “encryption,” you might think of mysteries or spy movies. Certainly, it may be more closely associated with such topics that are not everyday. However, “encryption” is actually something that is essential to our daily lives.

We enter passwords on the internet or apps, and input PIN numbers at banks, but all of these are supported by “encryption technology.” Furthermore, it is also used for the security of credit cards. Without encryption technology such as “RSA” and “Elliptic Curve Cryptography” that support modern society, civilization as we know it today would not be possible.

Cryptography was gradually becoming more and more closely related to mathematics. In the cryptographic techniques mentioned above, “RSA” is related to “factorization” and “Elliptic Curve Cryptography” is related to “Elliptic curve,” which is exactly mathematics itself. Factorization” is something that everyone learns in school, and many people might have felt what such calculations mean, but in fact it is used as a cryptographic technique.
Furthermore, the history of “encryption” is also a history of “sealing” and “silence.” This is because the essence of encryption technology lies in keeping it unknown. While “RSA” and “Elliptic Curve Cryptography” are encryptions for which it is okay if their mathematical mechanisms become known, in human history from ancient times to modern times, it has been important that “how they cracked the opponent’s encryption” or “the fact that they cracked the opponent’s encryption” does not become known to the opponent.

That’s why the history of “encryption” tends to be buried.
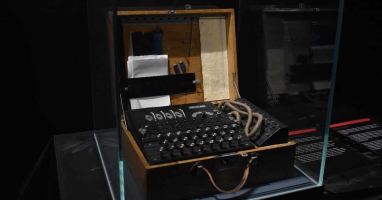
The most famous story of code-breaking in history is probably the decipherment of the German military encryption machine “Enigma”. The brilliant mathematician Alan Turing who deciphered Enigma is also known as the “Father of the Computer”.
However, the fact that he deciphered “Enigma” was kept a state secret for a long time, so it took some time for Alan Turing’s achievements to become known. It is said that his decipherment of “Enigma” saved the lives of more than 14 million people, but Alan Turing himself couldn’t endure the prejudice against “homosexuals” and tragically committed suicide. The achievement of deciphering “Enigma” was not revealed until after his death.
There is a movie called “The Imitation Game” based on his activities, so I recommend you watch it.
In this book, Simon Singh, known for works such as “Fermat’s Last Theorem,” carefully explores the history of cryptography, which is often kept secret.

Simon Singh always depicts the human drama behind the topics he covers, and this book is no exception. Especially when it comes to “codes”, which has many buried facts, various “little-known episodes” are incorporated. It can be read as an interesting story.
Basics of “Code Decryption” from Ancient Times
While today “codes” have become a field of “mathematics”, in the past, “linguists” were the ones who worked on code decryption. And the technique they used for decryption was called “frequency analysis”.

Before advanced encryption techniques utilizing mathematics were developed, the basic method of encryption was to replace each alphabet of a message with another alphabet based on some rule. For example, in the sentence “good morning,” each alphabet “g,” “o,” “d,” “m,” “r,” “n,” and “i” could be replaced with a different alphabet based on a certain rule, making the message indecipherable at first glance.
However, this type of encryption method had a significant weakness, which could be exploited using “frequency analysis.”

For example, the most frequently used alphabet in English sentence is known to be “e”. This means that no matter how you convert an English sentence, the most frequently appearing letter in the sentence will be likely to be “e”.
In this way, cryptography was deciphered using linguistic knowledge.
This method was not only used for cryptography, but also for deciphering ancient languages. “Ancient characters” are similar to ciphers in the sense that they are regular but unreadable and this is also discussed in the book.

Some ancient characters have been deciphered thanks to hints like the famous “Rosetta Stone,” while others have been decoded with no clues at all. However, there are still ancient characters that cannot be read. Will humanity be able to decipher all of them someday?
From Linguists to Mathematicians
Nowadays, mathematicians use their knowledge to decipher codes, taking over the job that linguists used to do.

The most important concept in modern cryptography is “Public-key.” It was conceived to solve a problem that involves all existing encryption methods.
The biggest issue with encryption using character substitution is the “key distribution problem.” When substituting characters, there is a rule (key) that exists, but it was difficult to deliver that rule.
For example, let’s say we want to keep in touch with people who are far away via radio using encrypted text. However, we cannot transmit the substitution rule itself over the radio, as it may be intercepted by eavesdroppers. The whole point of encryption is to prevent this from happening, so using the radio to transmit the rule would be meaningless. Therefore, the common method was to send a codebook containing the substitution rules via mail.
However, if the same codebook was used repeatedly, the enemy might be able to decipher the code. This means that it was necessary to “regularly send a new codebook” to prevent this from happening.
This is called the “key distribution problem”.
Mathematicians tackled this problem and came up with a solution. This gave birth to “Public-key cryptography”, with “RSA” and “Elliptic Curve Cryptography” being examples of “Public-key cryptography”.
Let’s take a look at how “Public-key cryptography” works. To explain cryptography, we will use “Alice” and “Bob,” who always appear in cryptographic descriptions (I don’t know why “Alice” and “Bob” are always used).
First, let’s review the cryptography before “Public-key cryptography.” For example, let’s say Alice writes a letter to Bob. The letter is put in a box, locked with a key, and sent to Bob. However, Bob cannot open the box as the key is with Alice. Therefore, Alice has to send the key to Bob in some way. This is the “key distribution problem.”

On the other hand, this is how “Public-key cryptography” works. Alice writes a letter, puts it in a box, locks it, and sends it to Bob just like before. The key is still in Alice’s hands. Then, Bob locks another key on the box sent in locked condition. In this way, the box is now in a state where two keys, Alice’s and Bob’s, are attached to it.

Bob sends the box back to Alice. Alice removes only the key she attached, leaving the other key that Bob put on, and sends the box back to Bob. Then, Bob has both the “box locked with Bob’s key” and the “key”. This allows Bob to retrieve the letter from the box.
Did you understand how “Public-key cryptography” solved the “key distribution problem”? In other words, by “both parties locking a box with keys”, the step of “sending the key” becomes unnecessary. This allows for both the “security of the letter in the box reaching the recipient safely” and the “convenience of not needing to send the key” to be achieved by a “cryptographic”.
All that’s left is to implement the above model using some mathematics. “RSA” uses “factorization” and “Elliptic Curve Cryptography” uses “Elliptic curve” to achieve this.
For example, RSA works like this:
Prepare two “enormously large prime numbers A and B.” Then, let’s call the number obtained by multiplying A and B “C”.
If we use a computer, we can instantly do a calculation like “A×B=C”. However, even with a computer, factorization such as “C=A×B” takes a terribly long time. It seems that with the processing speed of current computers, it takes much longer than the age of the universe to decrypt a message used “RSA”. In this way, it is “RSA” that cryptography uses the mechanism of “factorization taking an incredibly long time”.
Quantum Computer and Quantum Cryptography
Now, the truth is that “RSA” is in a bit of a crisis. This is because the development competition for “quantum computers” with processing speeds that cannot be compared to current computers is intensifying.

It may still take some time for quantum computers to become practical, but if they are developed, it’s already known that RSA encryption will be cracked in an instant. While there are other encryption technologies besides RSA, breaking RSA, which significantly ensures our daily safety, would be a serious problem.
However, this book also talks about the future prospects beyond that, which is quantum cryptography.
As explained earlier, RSA is an “encryption that is decryptable but practically impossible to decrypt with current computer speeds.” However, quantum cryptography is different. It is “theoretically considered absolutely impossible to decrypt.” Quantum cryptography was inspired by the knowledge of a field in physics called “quantum mechanics,” and it is said that “if quantum cryptography is decrypted, there must be some flaw in quantum mechanics.” At present, there are no theoretical flaws in quantum mechanics, so quantum cryptography is also considered absolutely impossible to decrypt.

I cannot explain the mechanism of “quantum cryptography” briefly, but I can tell you what makes it unique.
All previous encryption technologies were “unaware if they were being intercepted”. For example, in the case of Alice and Bob mentioned earlier, even if someone stole the two-keyed box in transit, forcibly pry opened it to read Alice’s letter without getting caught, and then closed the box and sent it as if nothing happened, Alice and Bob would not have noticed anything. Of course, in actual encryption technology, “the box will not open without the key,” so there would be no problem even if the box was stolen in transit. However, in any case, it is unclear whether it has been stolen or not.

However, “quantum cryptography” is different. If it is intercepted during delivery, there will always be a trace left behind. You can imagine it like “if someone try to force open the box with something other than the correct key, the paint inside the box explodes as soon as it is opened.” No matter how much they try to restore the key, traces of the paint will remain in the box, revealing that it has been intercepted.
With “quantum cryptography,” we can choose not to use the Public-key if there are traces of interception. And by using a Public-key with no traces of interception to encrypt the message, we can safely send and receive messages.

Toshiba has already announced that they will “commercialize quantum cryptography.”
We don’t know what will happen in the future, but if “quantum cryptography” becomes practical and widespread, even if “quantum computers” appear, we may be able to live in a world without security concerns.
Conclusion

This book covers various topics about “cryptography” from ancient times to modern day. It’s a great work, as expected from Simon Singh.
At the end of this book, there is a challenge from the author called “the toughest cipher in history”. It was already solved by a group of five people in Sweden after a year, but if you have time to spare, why not give it a try?

Published Kindle books(Free on Kindle Unlimited)
“The genius Einstein: An easy-to-understand book about interesting science advances that is not too simple based on his life and discoveries: Theory of Relativity, Cosmology and Quantum Theory”
“Why is “lack of imagination” called “communication skills”?: Japanese-specific”negative” communication”



コメント